Traefik Hackaethon Is a Wrap

Traefik Labs inaugural Traefik Hackaethon is a wrap. The event took place over three days on a Discord server that included contributors from around the world. Over 50 individuals joined the event and contributed several new plugins for Traefik, multiple bug fixes for Yaegi, and new features and capabilities for Traefik itself. This event was the first time Traefik Labs officially organized a hackathon. We couldn’t be more pleased with the collaboration between first-time contributors and long-time maintainers within our community.
Contributions Are Welcome Here
There are two distinct categories of contributions for this event: new plugins for Traefik Pilot and pull requests for our open source projects Traefik and Yaegi. Over a dozen individual contributors created new plugins, and we were pleasantly surprised by contributions to our open source projects in the form of new features, bug reports, and other improvements.
In this post, I’ll cover the contributions that the team was most impressed with and which were awarded the grand prizes. In addition to the grand prizes, several others deserve mention for their collective efforts, and I’ll cover those too! I want to give a special thanks to the engineering team at Traefik for engaging with the community and working with them to bring their ideas to life.
The entire team is looking forward to the next time we do this, and I’ll talk a little bit about that at the end of this post.
The Grand Prizes
One of the newest features of Traefik is support for adding customized functionality to the processing of requests handled by the Traefik Proxy. These are called Traefik Plugins, and nearly all ten bounties were claimed by our contributors! Each of the grand prizes went to a team or individual who contributed a plugin. The second prize has a bit of a caveat attached to it, but more on that later.
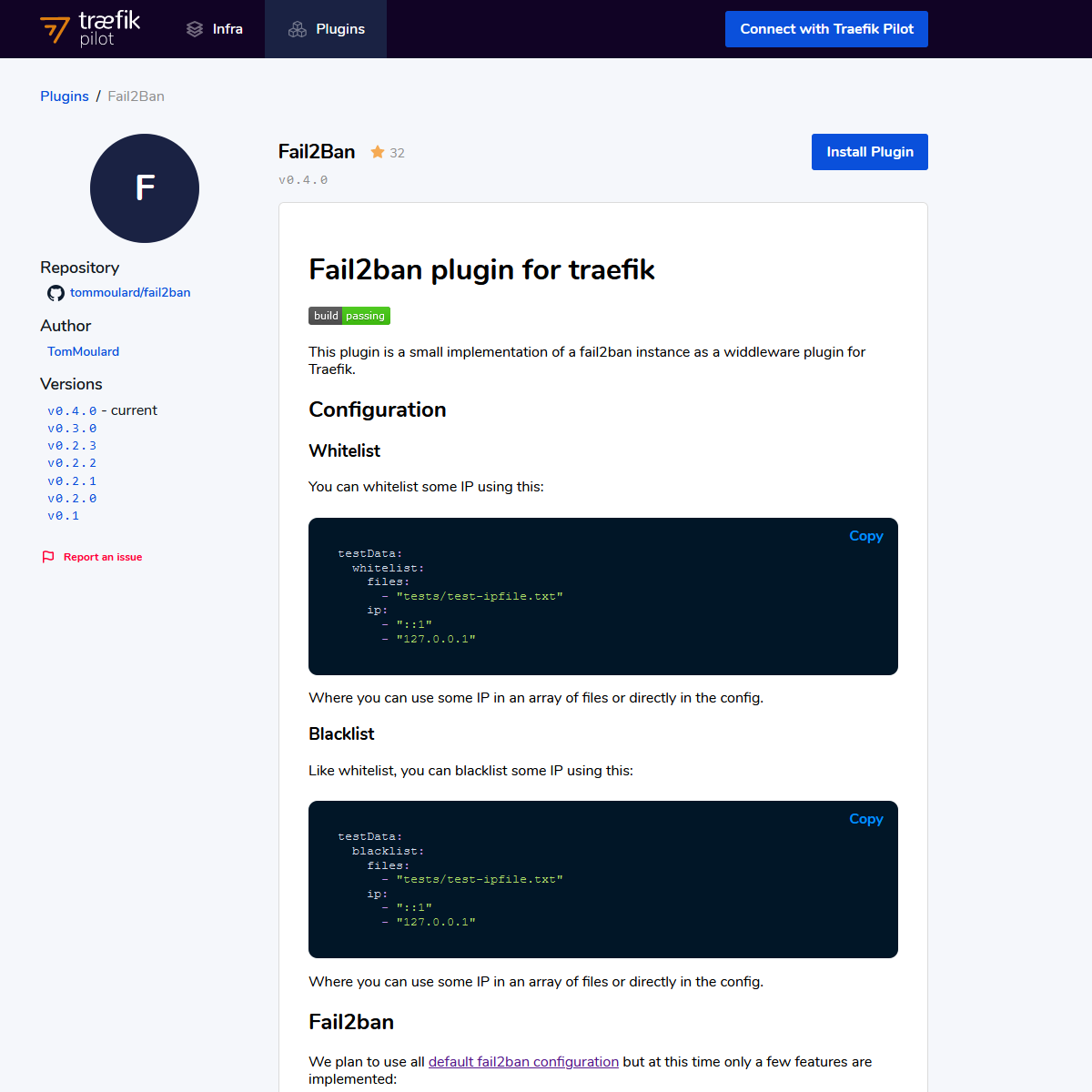
First Prize - Team Fail2Ban
https://pilot.traefik.io/plugins/605afbaaa5f67ab9a1b0e51c/fail2-ban
The first prize went to a team that was formed by a few contributors who had earlier worked on another plugin named Header Transformation (more about that below). One of the contributors not only produced a great blog post about their experience with the event, but they came together to create a handy plugin that will block requests originating from a source that fails to authenticate after a specific number of times. While the concept of Fail2ban isn’t necessarily new, nor is the implementation of it within a reverse proxy, this is the first time it’s become accessible without the use of external dependencies, complex iptables, or integrations with commercial packages. The implementation is complete and functionality impressive, given the tight deadlines and scope of the plugin. Thank you to Tom and the team for putting together two great plugins.
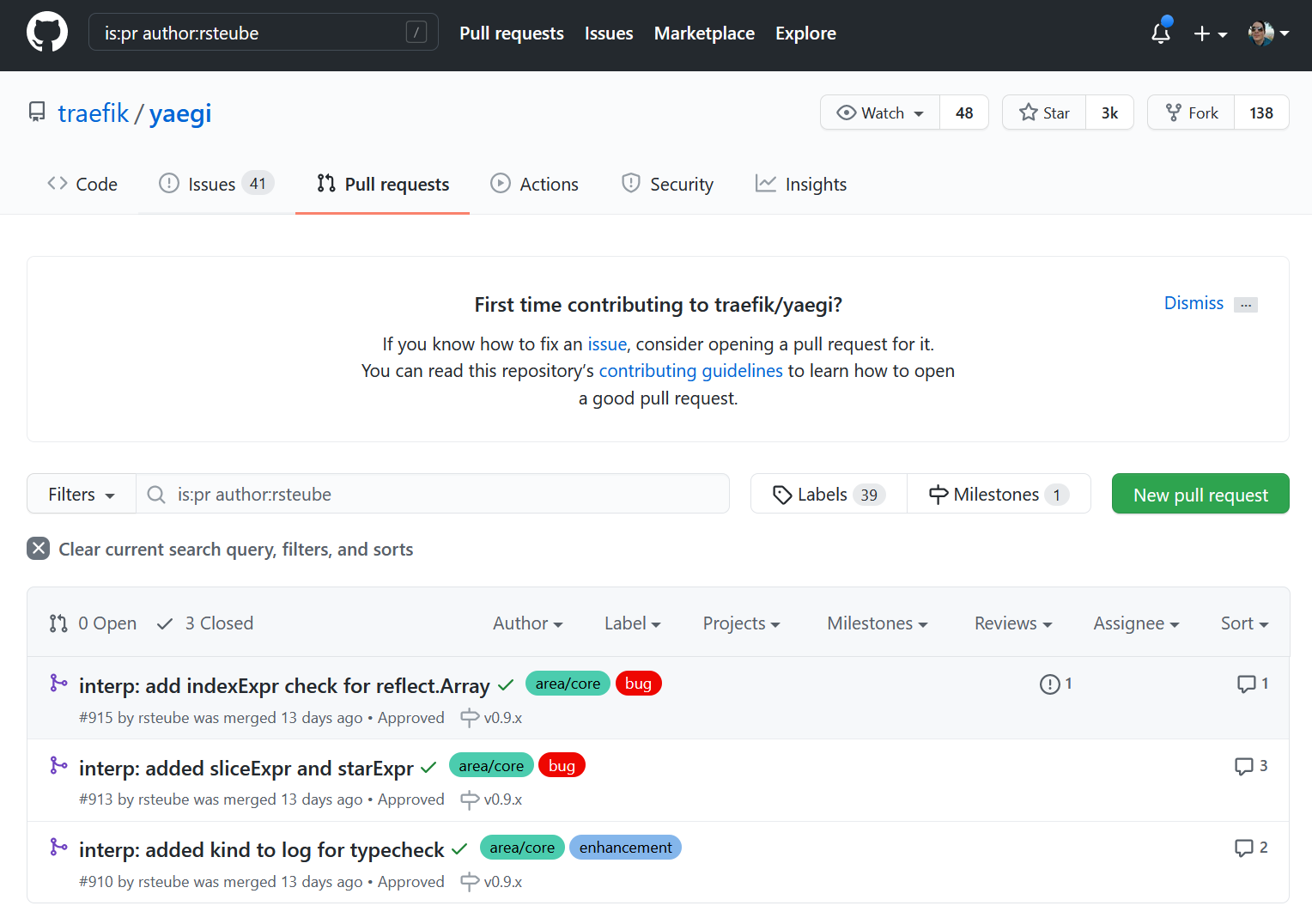
Second Prize - Team Brotli
https://github.com/traefik/yaegi/pulls?q=is%3Apr+author%3Arsteube
This plugin (that is still in progress) gets the second place award after the creator worked to implement a compression algorithm ported entirely over to Go, which coincidentally helped us bring even more compatibility to our runtime Go interpreter Yaegi. When we kicked off this Hackathon, we knew that the underlying engine that interprets code in real time, usually compiled, is still considered experimental. That didn’t stop this contributor. He worked all three days with Marc, the Yaegi project lead, to identify and fix numerous issues they found while incorporating the ported compression algorithm. This work led to several PRs and improvements made by the author and the Yaegi team. While the plugin wasn’t eligible for the plugin bounty, we felt his contributions to the Yaegi project were so impactful that this contributor deserved the second grand prize.
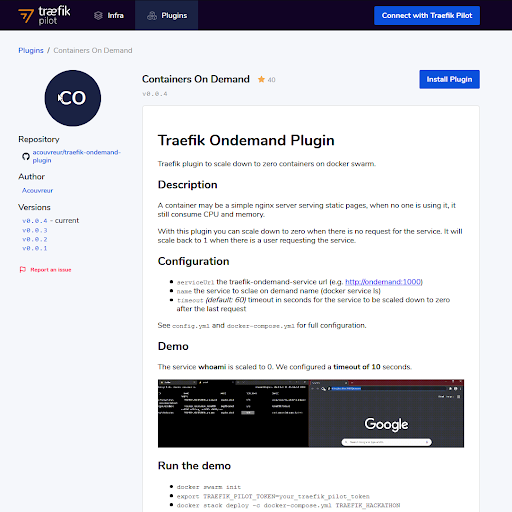
Third Prize - Team Containers On-Demand
https://pilot.traefik.io/plugins/605afbdba5f67ab9a1b0e53a/containers-on-demand
Imagine being able to scale up services from zero with Traefik when the load balancer receives a request. Two developers on this team hatched this idea together after discussing the concept and built a service that integrates with Docker Swarm to interact with the Docker API. The judges felt this plugin deserved the grand prize for two distinct reasons: First, developers’ persistence in finding a solution that works given the design constraints; and second, their creativity in deciding what to build. The plugin engine was created for users to be creative and bend Traefik in ways the developers at Traefik Labs might never have considered. This team’s contribution fits nicely into the vision the team had.
Plugin Bounties
Each of the above plugins was awarded a bounty (except for Brotli, since it’s technically still a WIP), but there are a few plugins that deserve mention.
Traefik Fault Injection
https://pilot.traefik.io/plugins/605afbe2a5f67ab9a1b0e53e/fault-injection
Purposely introducing faults and errors into an environment is a practice known as chaos engineering. This plugin allows for failures to be induced programmatically via the load balancer. It can be used to purposely inject failures of a specific type and rate to any service. Teams that are looking to build for resilience and solutions engineers who are looking to induce failures without having to modify application source code may find this plugin useful.
Header Transformation
https://pilot.traefik.io/plugins/605afbd5a5f67ab9a1b0e537/header-transformation
Authored by Team Fail2ban, this plugin allows for headers to be modified based on simple regex-based rulesets: Set, Rename, Del, and Join. Using these rules, operators can modify headers sent from the client before they reach their service destination.
Datadog Event
https://pilot.traefik.io/plugins/280005610925195785/datadog-event
Operators who install this plugin may generate an event in Datadog when a response code or contents matches a regex-based rule.
Open Source Contributions
We saw several PRs opened against Yaegi and Traefik Proxy. These included bug fixes, documentation improvements, new features, and capabilities. Below are two of the larger pull requests proposed, and while they’re both incomplete, we want to thank the authors for their contribution and hard work.
Exponential Backoff for Retry Middleware
https://github.com/traefik/traefik/pull/7460
The author of this PR initially tried to implement a DynamoDB cache plugin, but he encountered a limitation with the AWS SDK and Yaegi. Instead of giving up, he jumped right into an open issue and started working with the open source engineers at Traefik to develop a solution.
FluentD Log Hook
https://github.com/bearstech/traefik/pull/1
This work is incomplete, but it seems to be ninety-percent there. This feature, when merged, would allow operators of Traefik to directly connect access logs to a log exporter, rather than having to use a log scraping implementation. We’re looking forward to seeing this feature finished up and opened as a PR.
And ... It's A Wrap

We couldn’t be more excited to see the contributions and collaboration at our first Traefik Hackaethon. We’ll be doing this again next year and have already started planning for the spring. In the meantime, our team would love to hear from you on ideas for themes and bounties. We’ve opened a thread on our community forums to discuss what you’d like to see the next time.
Thank you to all the participants, and your contributions to the Traefik ecosystem are sincerely appreciated. We can’t wait to see what you’re going to build next.