OpenClaw is Having Its Enterprise Moment, But Application-Layer Governance with NemoClaw Isn't Enough
There is a specific kind of moment in enterprise technology that repeats itself with uncomfortable regularity. Something built for individuals gets handed to organizations, and nobody has figured out the governance story yet.
It happened with the cloud. The moment Amazon launched EC2, developers started spinning up servers on personal credit cards. It took years for the enterprise to catch up on IAM policies, cost governance, and audit trails. The capability arrived long before the controls did.
It happened again with SaaS. By the time IT leaders understood what Dropbox was doing on their networks, half the organization had already stored sensitive documents on personal accounts. Shadow IT emerged as a category because the tools moved faster than the institutions.
That moment is here again with AI agents. And the signal worth watching most closely right now is what just happened to OpenClaw.
From Developer Favorite to Enterprise Infrastructure
OpenClaw started as an open-source personal AI agent gateway, a tool that lets individual developers connect chat applications to AI models and local tools. It caught fire. 247k+ GitHub stars. 47k+ forks. The kind of organic adoption that does not happen because of marketing, it happens because engineers found something genuinely useful and started sharing it.
The creator, Peter Steinberger, joined OpenAI in early 2026. And then NVIDIA did something that tells you everything about where agentic AI is headed.
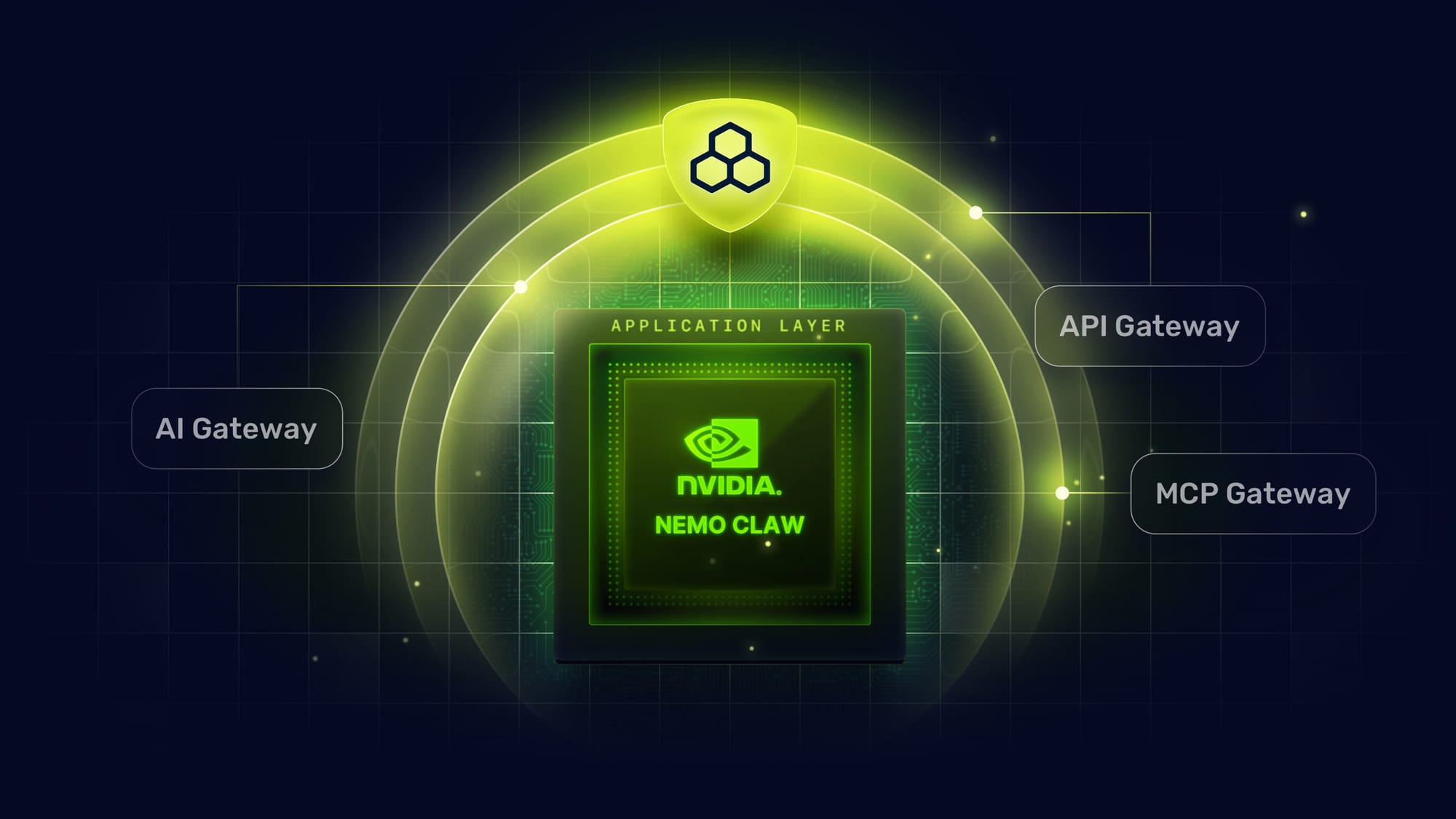
At GTC 2026, Jensen Huang unveiled NemoClaw, describing it as "30 years of NVIDIA computing, distilled into an agent platform." NemoClaw builds on what OpenClaw built for individuals and adds enterprise-grade architecture on top: multi-agent orchestration, hierarchical task delegation, signed skill registries, role-based access controls, audit logging, and deterministic logic for verifiable tool call sequences. It supports the Model Context Protocol natively, connects to the Agent-to-Agent protocol, runs on Nemotron models at 30B, 120B, and 500B parameter scale, and integrates with Salesforce, Cisco, Adobe, Google Cloud, and CrowdStrike out of the box.
This is not a library. Not a framework. It is the operating system of agentic computers — open-source under Apache 2.0, with a paid tier for managed infrastructure and compliance tooling.
This is the enterprise moment. And it changes what every CISO, Chief AI Officer, and platform architecture leader needs to be thinking about right now.
What NVIDIA Got Right
The governance capabilities built into NemoClaw are real and meaningful.
Enterprise role-based access controls on agent identities, so the finance agent and the customer support agent do not share credentials or capability sets. Signed skills, so the tools available to agents cannot be silently modified by a supply chain compromise. Step-level policy checks before every tool invocation, so an agent cannot take an action the platform has not explicitly authorized. Comprehensive audit logging at the orchestration layer.
These are not checkbox compliance features. They represent serious architectural thinking about what makes agentic AI deployable inside organizations with actual security programs.
NemoClaw's launch confirms what practitioners have been arguing for two years: enterprise agent governance is a mainstream requirement, not a niche concern. NVIDIA, with all its platform credibility and hardware distribution power, is now building it into a flagship product. That is a meaningful signal.
But the existence of application-layer governance does not imply complete governance. That distinction is where the real architectural question begins.
One Governance Layer Is Never Enough
The foundational principle of enterprise security is Defense-in-depth: no single control is trusted to stand alone. Every meaningful security architecture deploys independent enforcement at multiple layers, so that a failure, bypass, or compromise at one layer does not collapse the entire posture.
This principle predates AI agents by decades. It is why organizations run both endpoint detection and network monitoring. It is why zero-trust architectures do not simply trust identity at login and then grant full access. It is why the firewall analogy holds so cleanly: application firewalls understand business logic and enforce policy with context, but network firewalls enforce at a layer the application cannot reach. The answer has never been one or the other. It has always been both.
NemoClaw's governance is application-layer governance. Its guards operate inside the agent runtime, coupled with the agent itself. The access control policies, the signed skill checks, the deterministic logic engine, the audit logs, all of these run within the same process that is being governed. A compromise to the agent also compromises the guards that are governing it. This is not a design flaw. It is the nature and limitation of tightly coupled application-layer controls, and it is exactly what Defense-in-depth says is necessary but not sufficient.
Consider what happens when a NemoClaw agent makes an inference call to a Nemotron model. The request leaves the agent runtime and travels across the network to an endpoint. At that moment, one cannot be sure whether NemoClaw's governance allowed it because it's a legitimate request or because its governance was also compromised along with the agent. Its governance might allow the payload to contain PII from a customer database. It might be a prompt injection payload embedded in a tool response. Also, application-layer controls cannot enforce a token budget at the network layer before GPU cycles are consumed. It cannot verify that the specific parameters in an MCP tool call, not just the tool class, but the actual values, conform to the organization's security policy.
This is not a gap unique to NemoClaw. It is inherent to any system that governs from the inside out. And it is precisely the gap that the defense-in-depth principle exists to close.
The Triple Gate: Defense-in-Depth Made Concrete
Applying Defense-in-depth to NemoClaw deployments means identifying the distinct traffic vectors generated by agents and placing independent enforcement at each.
NemoClaw agents generate three kinds. Every inference call to a language model. Every MCP tool invocation. Every request to the agent management and orchestration APIs. Three vectors, each carrying different risks, each requiring its own enforcement point.
This is the architecture Traefik Hub's Triple Gate Pattern addresses directly.
The AI Gateway sits in front of every inference call a NemoClaw agent makes, to Nemotron, to OpenAI, to Anthropic, to any model endpoint. It runs a four-tier safety pipeline: pattern-matching for injection signatures and PII formats, real-time PII redaction, NVIDIA Safety NIMs for topic control and jailbreak detection, and response-side hallucination scoring. This pipeline runs at the traffic layer, independently of NemoClaw's internal guardrails. If the agent runtime is compromised, the AI Gateway continues to run. It also enforces token rate limits per agent, per team, and per API key, a hard network-layer stop that operates before GPU resources are allocated.
The MCP Gateway sits in front of every tool invocation. NemoClaw's role-based controls determine which tools an agent role is permitted to use. The MCP Gateway enforces at the parameter level, the specific values being passed, the specific data being accessed, the specific operations being requested, against infrastructure-layer policy that exists independently of the agent runtime. This is the enforcement layer that catches tool-call escalations even when the tool call itself is legitimately authorized. Refusals are returned as structured responses that NemoClaw agents handle gracefully, without crashing workflows.
The API Gateway governs the NemoClaw management plane itself, the agent configuration endpoints, monitoring interfaces, and orchestration APIs that constitute the control surface of any NemoClaw deployment. These endpoints are attack surfaces in their own right. The API Gateway enforces authentication, rate limiting, schema validation, and WAF rules against the OWASP threat model, independent of anything running inside the NemoClaw runtime.
Three gateways. Three enforcement points. Each layer is independent. Each layer covers attack surfaces that the others do not reach. This is Defense-in-depth applied to the specific topology of enterprise agent deployments.
Four Scenarios That Illustrate the Need for Defense-in-Depth
Defense-in-depth only has value if it addresses real attack vectors. These four scenarios are representative of what enterprise deployments will face.
1. Prompt Injection via Tool Response
An agent calls an external tool and receives a response. Embedded in that response is a carefully crafted instruction designed to redirect the agent's next action. NemoClaw processes this at the application layer after it has already been ingested by the runtime. The AI Gateway intercepts the tool response before the agent sees it, running it through the safety pipeline at the traffic layer. The injection never reaches the runtime.
2. Token Drain via Recursive Calls
A misbehaving agent triggers recursive inference loops. NemoClaw's resource budgets are soft limits enforced inside the runtime. If the runtime is in a problematic state, those budgets may not hold. The AI Gateway's token rate limiting is a hard stop at the network layer, applied before inference requests reach the GPU cluster. No compute is consumed, regardless of the runtime's state.
3. MCP Tool Escalation via Parameter Crafting
An agent constructs a tool call in which the tool itself is authorized under its role, but the parameters are crafted to exceed the intended scope. NemoClaw's role-based controls authorize the tool class. The MCP Gateway validates the specific parameters against infrastructure-layer policy at the network layer, independently of the runtime. The escalation attempt fails at the enforcement point closest to the tool.
4. PII Leakage in Inference Responses
A model response contains customer personally identifiable information that was present in the context window but was not intentionally requested. NemoClaw logs the interaction after the fact. The AI Gateway operates bidirectionally on the traffic itself, redacting PII in both requests and responses before they move further in the chain. Whether the agent requested the data or received it incidentally, anything that crosses the network gets inspected and sanitized before it travels further.
In each scenario, the enforcement point that stops the incident is independent of the agent runtime. That independence is exactly what Defense-in-depth requires.
The Architecture Choice That Only Gets Made Once
When enterprise leaders evaluate NemoClaw deployments, the real decision is not which agent platform to use. NemoClaw is genuinely compelling and will see serious adoption. The decision is whether to deploy it with only application-layer governance or with the full defense-in-depth posture demanded by the threat landscape.
That choice compounds over time. Teams that build governed agent infrastructure now, with the agent runtime owning application-layer governance and the Triple Gate owning traffic governance, will move faster as the agent landscape expands. Their security posture does not depend on any single component being uncompromised. Their compliance story holds up to auditors who understand Defense-in-depth. Their cost controls operate at the network layer, where they cannot be bypassed by a misbehaving agent.
Teams that deploy with only application-layer governance will eventually encounter an incident that exposes the gap. Retrofitting infrastructure controls into a production system under pressure is the most expensive way to build them.
What This Means for Platform Decisions
For security leaders evaluating agent deployments, the question to put to architecture teams is direct: does our governance posture reflect Defense-in-depth, or does it rely on a single enforcement layer inside the agent runtime? If the runtime is degraded or compromised, what remains?
For Chief AI Officers enabling agentic workflows at scale, the infrastructure layer is what enables scalable governance without becoming a bottleneck. A policy enforced at the network layer applies to every agent, regardless of which framework built it, which runtime runs it, or which vendor's model it calls. That universality is the difference between governance that scales and governance that requires a new exception for every new deployment.
For platform architecture leaders, the Triple Gate model maps cleanly to a separation of concerns that infrastructure teams already understand. The agent platform team owns the runtime governance. The platform infrastructure team owns the traffic governance. Neither depends on the other to do its job, and a compromise of one does not take down both.
The Broader Signal
NVIDIA building enterprise governance into NemoClaw confirms that the demand for governed agents is now mainstream enough to justify a platform-level investment from one of the most capital-efficient organizations in technology history. Jensen Huang does not build products for markets that do not exist.
What NemoClaw does not include, the API gateway in front of agent endpoints, the safety pipeline on inference traffic, the infrastructure-level MCP authorization, the token rate limiting at the network layer, is not an oversight. It is a scope decision. NVIDIA's business is silicon and model infrastructure. Agent governance at the traffic layer is a different problem, one that requires deep integration with Kubernetes ingress, API gateway protocols, and network-layer traffic management.
That scope decision is not a gap NVIDIA needs to fill. It is the natural boundary where the agent runtime ends and the infrastructure governance layer begins — the boundary where defense-in-depth becomes operational.
The organizations that understand this, that see NemoClaw's application-layer governance and Traefik's Triple Gate as two halves of a complete defense-in-depth posture, are the ones that will deploy AI agents at enterprise scale without discovering their assumptions were wrong after the fact.
OpenClaw had its enterprise moment at GTC 2026. Defense-in-depth is what turns that moment into a durable foundation.
To see how Traefik Hub's Triple Gate architecture provides infrastructure-level governance for NemoClaw deployments, see this blog post.




