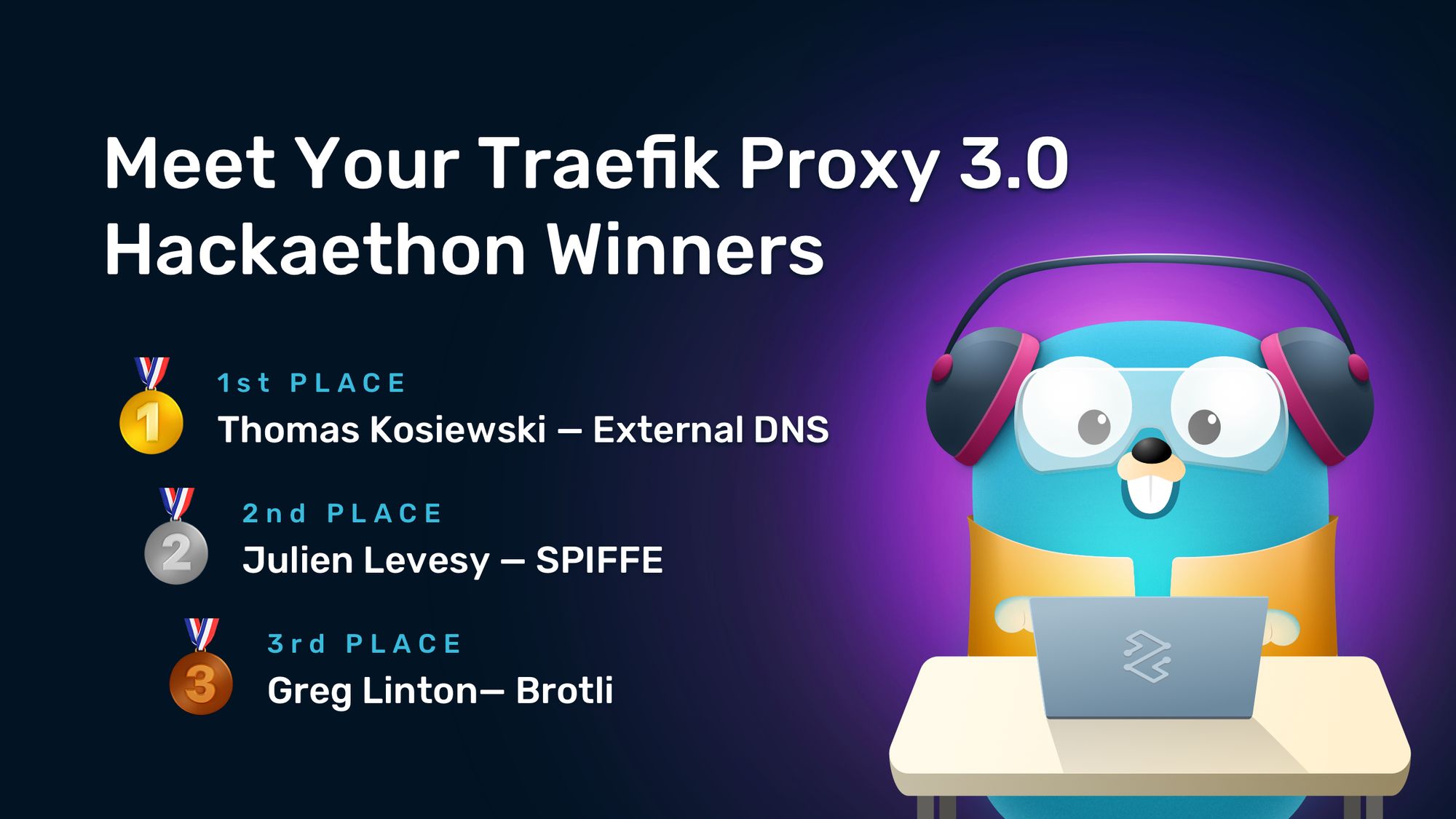
Kicking Off Traefik Proxy 3.0 With Style — Meet Your Hackaethon Winners
The Traefik Proxy 3.0 Hackaethon is officially a wrap!
This Hackaethon was an event very close to our hearts. Focused on building the next major release of Traefik Proxy, the Traefik Proxy 3.0 Hackaethon was designed to give the community the means to drive Proxy’s development and tackle long-awaited requests and performance improvements. For the first time ever, we allowed features to introduce breaking changes.
We were thrilled to see nearly 100 community members coming together to kick off building Traefik Proxy 3.0! During the hackathon, 16 projects were actively worked on and 11 completed projects were submitted. Some of the projects were particularly challenging, so we offered a $250 bounty as an extra thank you to the community members who helped.
Our judges carefully reviewed and analyzed the submitted projects, and we are proud to present the winners of the Traefik Proxy 3.0 Hackathon!
The winners
This Hackaethon was primarily focused on Traefik Proxy features targeting the v3.0 release that are much-anticipated and wanted by the community and were awarded a $250 bounty each. Participants who worked on most-wanted features had the chance to claim the bounty as well as win one of the top three prizes. After talking to all three winners, it was humbling for us to realize that — aside from the monetary incentive, of course 😏— the main motivation for them to join this Hackaethon was the desire to give something back to the Traefik Proxy community and to the product they’ve been happily using for years!
So, without further ado, please welcome the winners of the Traefik Proxy 3.0 Hackathon.
🥇 Grand Prize
Thomas Kosiewski — External DNS
Awards claimed: $1000 + $250 bounty + limited edition Hackaethon hoodie
Put your hands together for our Grand Prize winner, Thomas Kosiewski!
External DNS is a huge topic inside the K8s community. Integrating directly with it lowers users’ work and the barrier of using it together with Traefik Proxy. Thomas worked on a solution that fixes two open issues: using External DNS with a Traefik IngressRoute, and using the KubernetesCRD provider with External DNS.
We were very excited to see the solution Thomas created, which allows Traefik CRDs (IngressRoute / IngressRouteTCP / IngressRouteUDP) to be used with External DNS and to configure the DNS automatically when these Traefik resources are deployed in a Kubernetes cluster. Thomas opened the pull request for adding support for Traefik IngressRoute, IngressRouteTCP, and IngressRouteUDP directly in the External DNS repository.
Thomas’ project tackled a long outstanding and wanted issue with great added value for Traefik Proxy users. But this is not the only reason we awarded him the Grand Prize! The code Thomas submitted was clear and followed the requirements set by the Traefik Proxy maintainers; namely, it does not add a dependency to Traefik in the External DNS project. All in all, the collaboration was excellent, and it was our pleasure to work with him on this project.
Once again, congratulations on your big win, Thomas!
🥈2nd Place
Julien Levesy — SPIFFE
Awards claimed: $500 + limited edition Hackaethon hoodie
The winner of the second place is none other than our dear friend and ex-colleague, Julien Levesy!
Now, this was a submission that caught us by surprise. There has been no issue related to this contribution, and it is, in fact, a very niche feature. Nonetheless, we were happy to see trendy features making their way to Traefik Proxy! Julien made two submissions adding support for SPIFFE mTLS and support for SPIFFE mTLS between Traefik Proxy and backend servers. Julien’s contributions add a number of functionalities:
- Making Traefik usable in a SPIFFE environment
- Allowing Traefik to obtain a SPIFFE ID and validate the SPIFFE identity of the backends
- Making it possible to establish trusted connections between Traefik and the backends (mTLS)
These changes will make Traefik fully usable in a SPIFFE environment and, despite this being a particularly challenging implementation, Julien did a great job! The submitted issue offers detailed context and implementation guidelines, the code looks great, and it’s ready to be merged after a single review, so we are more than happy to award Julien with the second-place prize.
Thank you for the awesome work, Julien!
🥉3rd Place
Greg Linton — Brotli
Awards claimed: $250 + $250 bounty + limited edition Hackaethon hoodie
The third-place award goes to another bounty feature and its contributor, Greg Linton!
Support for Brotli compression algorithm is another long outstanding and community-wanted feature. In fact, a fix for this issue was first attempted during the previous Hackaethon, where a team was awarded the second-place prize for their work on adding support for Brotli compression as a Traefik Plugin. Unfortunately, the work on the plugin was not completed, and the plugin itself never became available. Needless to say, we were very excited to see Greg working on this feature!
Greg submitted a pull request that adds support for the Brotli compression algorithm to Traefik Proxy and enhances the Traefik Compress Middleware to be able to use the Brotli compression algorithm if the backend sends an uncompressed response, provided that the client supports Brotli compression.
Working with Greg was smooth sailing, as the whole collaboration was straightforward, and the only thing he required from our team was to confirm his assumptions. Greg’s code was clean and mergeable after a single review, and well deserved the third-place and bounty prizes!
Congratulations, Greg, and thank you for this excellent contribution!
Honorable mentions
Last but not least, we want to give a big shout-out to a couple of teams who made this hackathon special — the folks behind the LittleThingProject (Mathieu Hanotaux and Max Lerebourg) and team Servers Transport on TCP (Stephen Wambugu and Boye Olowoyeye)!
Mathieu and Max worked on three separate projects, one of which is a Traefik plugin that integrates a CrowdSec Bouncer, and is already up for grabs in the Plugin Catalog. Overall, the LittleThingProject team was very active and engaged, they brought life to the Hachaethon, and the Traefik Proxy maintainers had a wonderful time working with them!
Stephen and Boye worked on Server Transport on TCP Configuration. While the solution didn’t quite work by the hackathon’s deadline, it inspired some of our team members who joined forces to bring the PR to a successful conclusion.
It’s a wrap! What’s next?
The Traefik Proxy 3.0 Hackaethon was a wonderful experience for us as we got to work deeply with the community. Working with everyone was a delight, and we really hope to continue working with them in the future. A big thank you goes out to all participants for your fantastic work and ideas!
If you missed this Hackaethon but you still wish to contribute to Traefik Proxy 3.0, there’s always room for you! Currently, we have two ongoing projects that would benefit from your contributions:
Coming up next is KubeCon 2022, where we’ll celebrate Traefik Hub! Stay tuned for more news, and, if you’re attending, don’t hesitate to drop by the Traefik Labs booth to do a hands-on demo of Traefik Hub, pick up a limited edition t-shirt, or just say hi!