Reverse Proxy Explained: How It Works And When You Need One
Businesses around the world rely on reverse proxies for their cloud and bare-metal applications. Proxies, in essence, allow people accessing websites and services to do so with far less strain on their networks as well as their business's application.
Let's take a deeper look into what a reverse proxy is, how it differs from a standard, forward proxy, and why you should consider using one.
What is a reverse proxy?
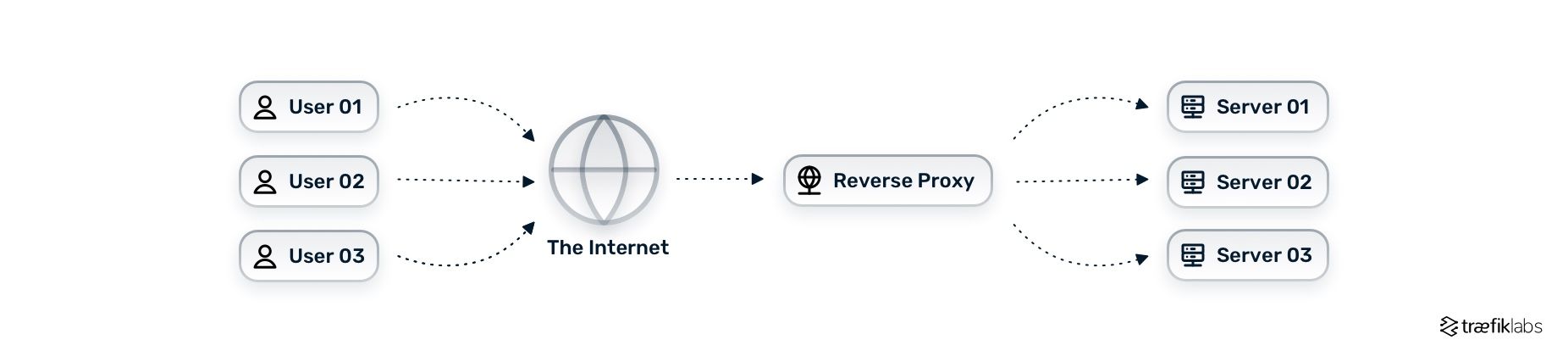
A reverse proxy is a piece of software that receives user requests and forwards these requests to the appropriate server. Many users target the same endpoint and at that very endpoint, you find a reverse proxy accepting and dispatching requests on behalf of the servers.
In simpler terms, a reverse proxy is like the old-school phone operator. Once upon a time, there used to be call centers and phone operators — callers would state the name and the address of the person they wanted to reach, and the phone operator would connect them. That is essentially what a reverse proxy does.
The difference between a reverse proxy and a forward proxy (proxy server)
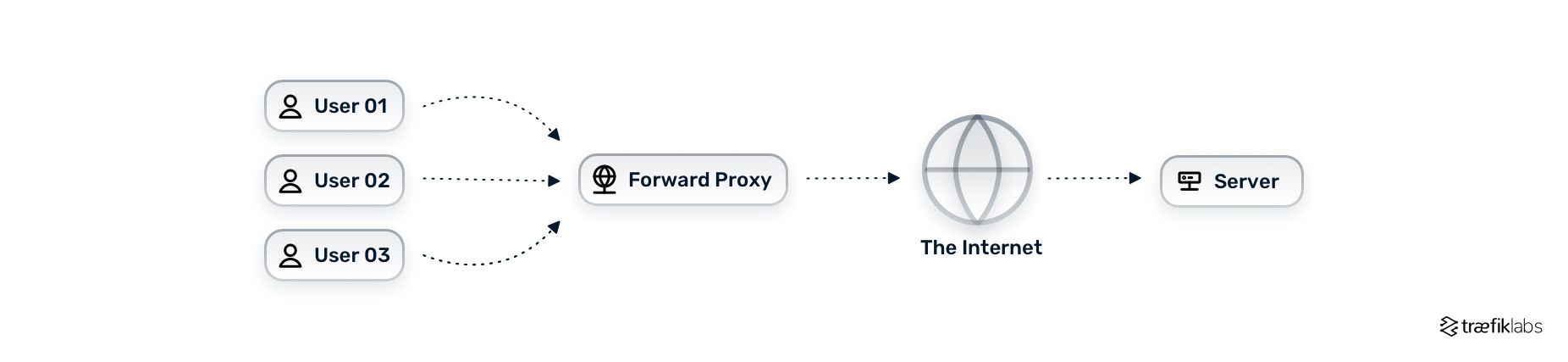
A forward proxy — also known as a proxy server, or simply, a proxy — is a piece of software that receives user requests and forwards these requests to the server on behalf of the user. Unlike a reverse proxy, in this case, there are many visitors using the same bandwidth. This way, the user does not directly connect to the internet but goes through a proxy server instead. Using a proxy server allows applications to implement caching, better access control, optimization of bandwidth, and much more.
Reverse proxy vs. load balancer
Based on the definition of reverse proxy we saw earlier, it is common to confuse a reverse proxy with a load balancer. Is a reverse proxy the same as a load balancer? Are there any differences? Can you use both at the same time?
The short answers are that they’re not the same and you can use them both. In a nutshell, load balancing is a feature of a reverse proxy.
The core function of a reverse proxy is to accept requests and forward them to the servers — without any additional logic or function behind it.
But, typically, reverse proxies embed different features, and load balancing is one of them. The reverse proxy accepts a number of requests, but instead of blindly pushing all requests to one server, it uses load balancing to balance the traffic across different servers. One way this is accomplished is by using the round-robin method, as seen in the diagram below.
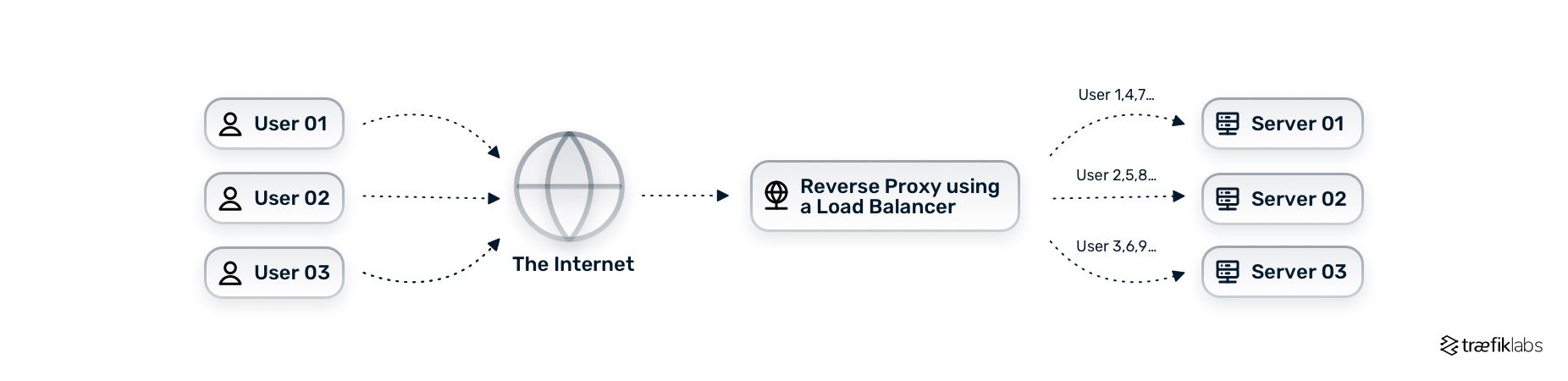
The round-robin algorithm is only one of many methods used in load balancing. Other algorithms take into account additional data, such as the server's response time, average requests-per-second, an existing session, etc., and send requests to the appropriate server based on this data.
What are the key features of a reverse proxy and why do you need one?
There are a number of reverse proxies out there offering freemium plans. Each solution offers a different set of features. Here is a quick list of core features commonly found in open source reverse proxies:
- Support for different protocols (e.g. HTTPS, TLS, HTTP/3, TCP, UDP, etc.)
- Load balancing
- Routing
- Rate limiting
- Authentication
- Request validation
You can check out the Traefik Proxy documentation for the full list of features and capabilities of our reverse proxy.
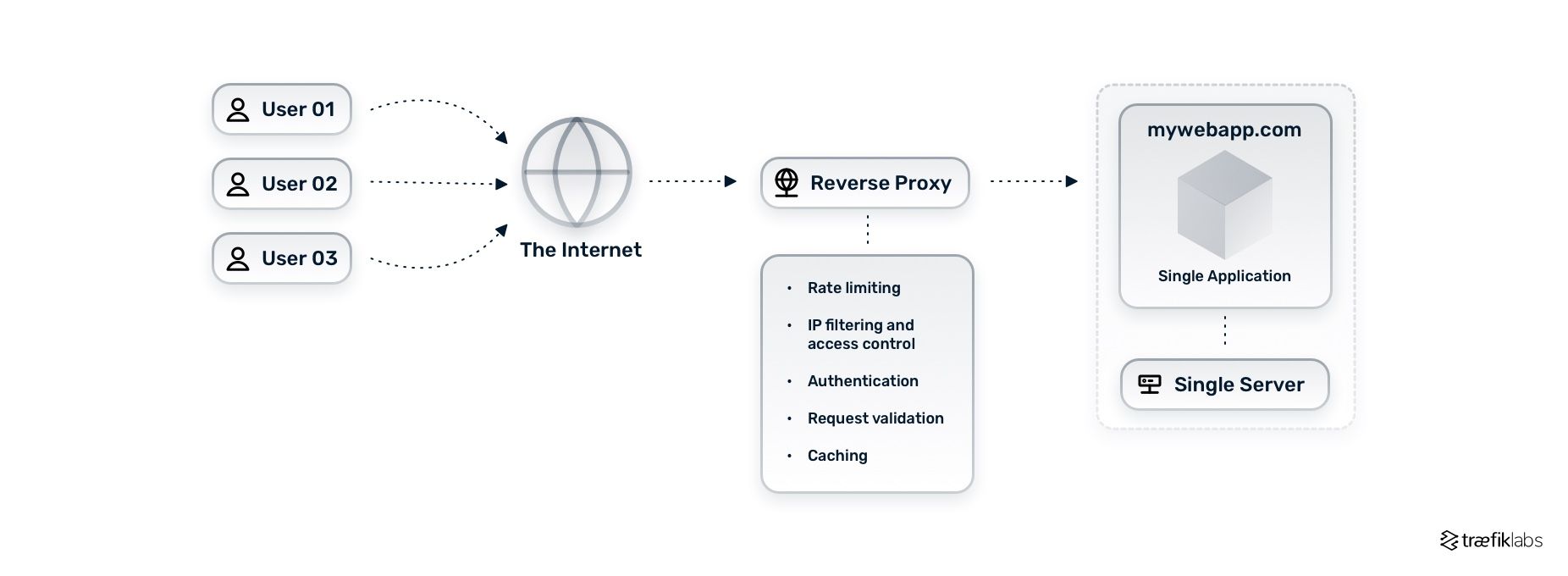
Additionally, reverse proxies receive user requests, find the appropriate server among a number of servers, and forward the user request to that server. Those of you using a single server may be wondering whether or not it makes sense to even implement a reverse proxy.
Before you move on thinking this isn’t right for you, it’s important to understand that reverse proxies can be useful, even in single-server scenarios with:
- Rate limiting
- IP filtering and access control
- Authentication
- Request validation
- Caching
Scaling the example we saw in the first scenario, let's assume the mywebapp.com business and, in turn, its website is growing. To accommodate the needs of this growing business, we add two more pages (or applications) to our main website — the /blog and /shop applications — as well as two more servers to handle the increased number of requests, as seen in the diagram below.
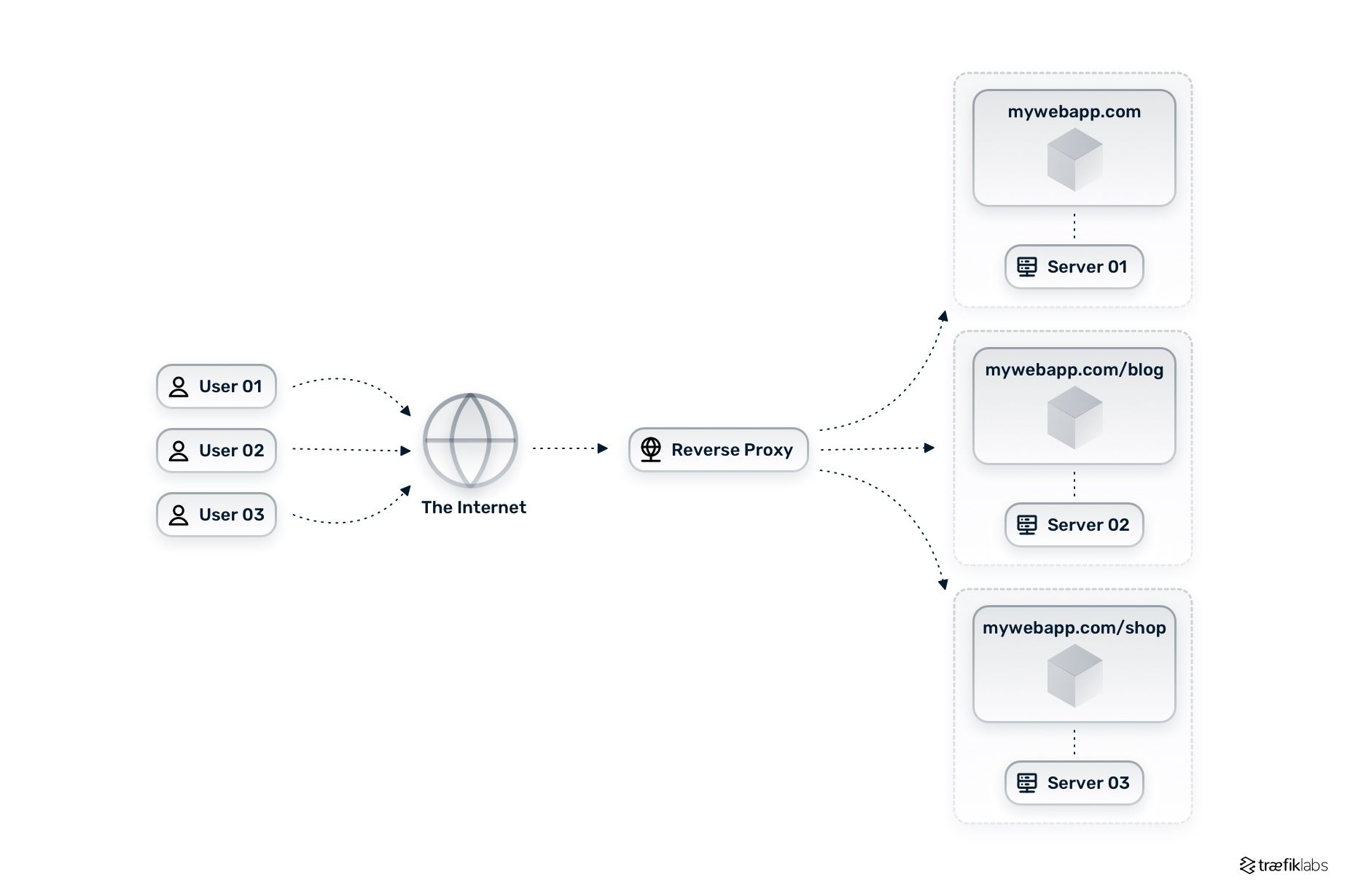
In this scenario, we utilize a reverse proxy and all its features leading to a number of benefits:
- Simplifying access control
- Reducing security risks when handling sensitive data
- Ensuring regulatory compliance
- Caching common requests
- Reducing response time
- Increasing scalability
Reverse proxy caching
Reverse proxies have the ability to store copies of the request data, that can be accessed later without the need to communicate with the server. Every time a user makes a request to a website or an application, the application needs to calculate the response to that request, and send it back to the user. Reverse proxy caching stores the result of the request, so it won’t have to ask again every time the server receives the same request from that specific user.
Certain benefits come with reverse proxy caching. First and foremost, using reverse proxy caching improves your application performance. Since the application doesn’t have to compute the response to the same request each time a user makes said request to the server, the application loads much faster. It’s also important to note that in the event of the network is interrupted, cached data can be used to fulfill user requests. Overall, reverse proxy caching solves a number of issues related to:
- Database response time
- CPU limitations
- Inconsistent response times
- Increased API bills
When is it time to invest in an enterprise-grade reverse proxy?
Although open source reverse proxy solutions can offer an impressive set of features that cover a wide variety of needs, there is always a natural limit.
When scaling applications, moving to an enterprise solution is highly beneficial, giving you a wide variety of features including but not limited to:
- Higher level of authentication
- Wider variety of metrics
- Greater options and configurability
- Third-party integrations for tracing and logging
- Personalized support
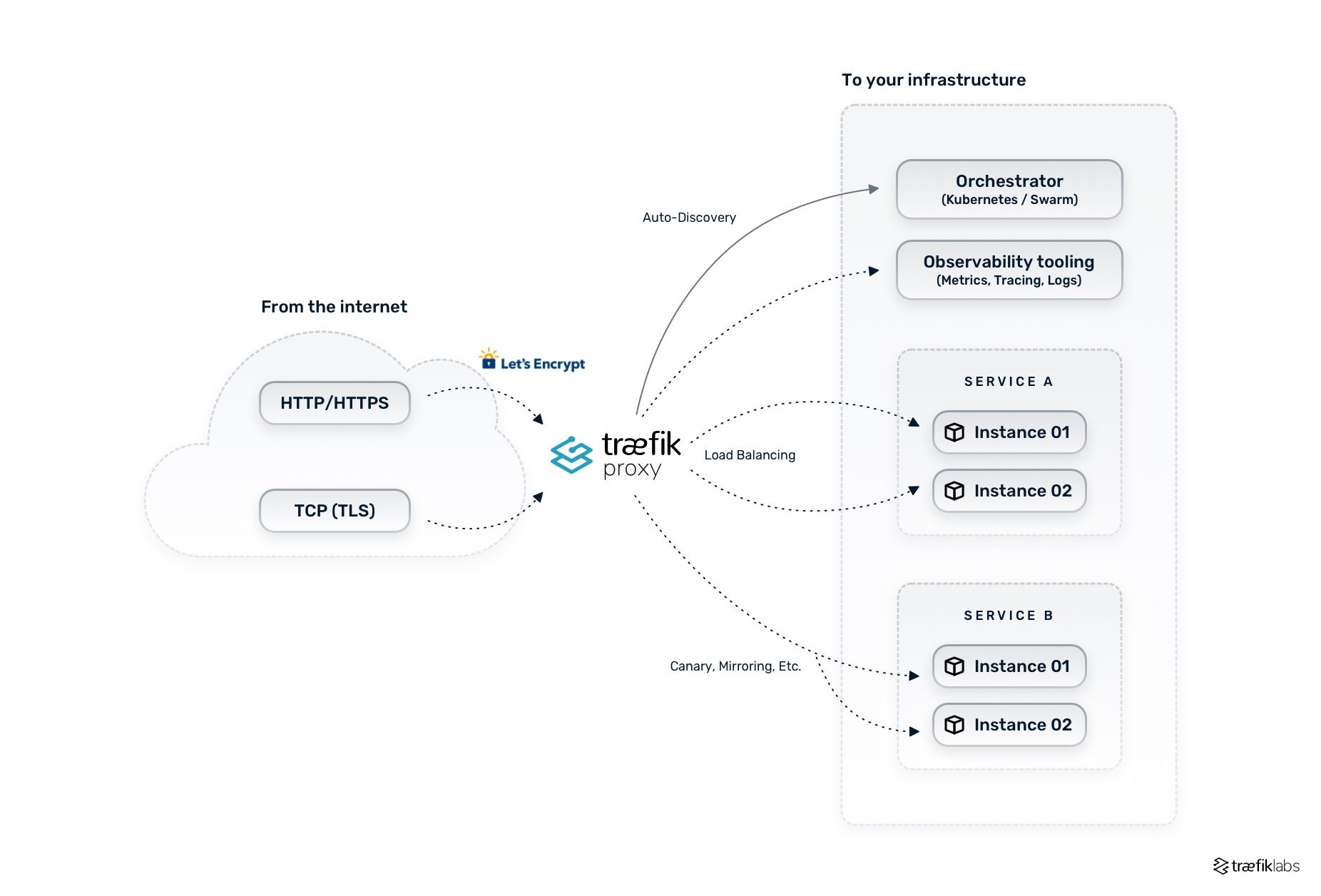
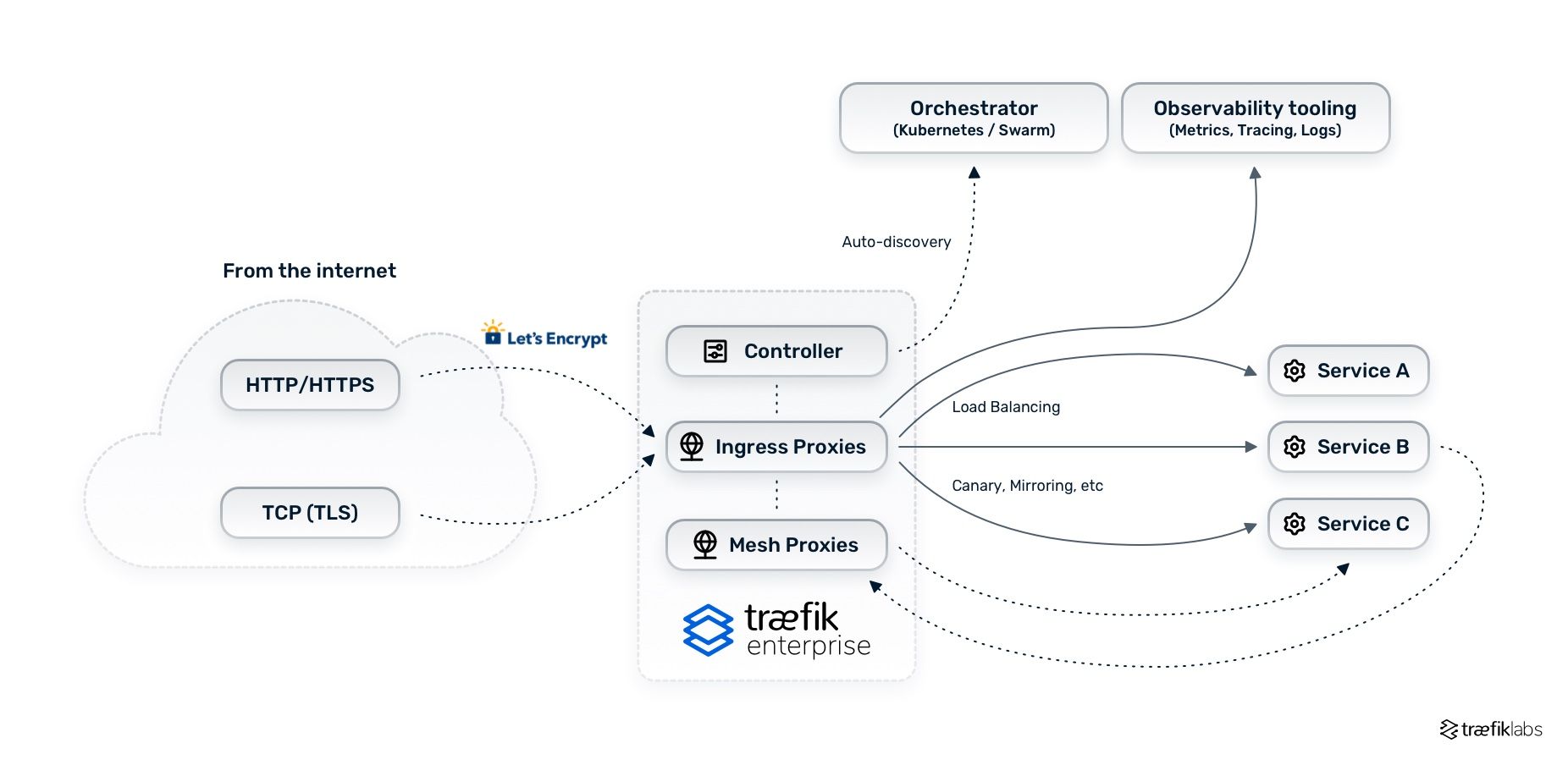
In the two diagrams below you see the architecture of an open source reverse proxy vs. an enterprise networking solution.
If you are looking for more information on how an enterprise networking solution can help successfully scale your applications, read more here.


