Traefik 1.6 — Get Our Latest tetedemoine!

After 3 months of development, we are thrilled to announce the fresh new release of Traefik: 1.6, codename “tetedemoine”.
We merged 168 pull requests from more than 43 contributors! A huge thanks goes out to each of you who helped on this new version 😘.
The full changelog can be found here but here are some new features we want to highlight:
Let’s Encrypt Wildcard Certificates

This was a long-awaited feature; we are proud to announce that we officially support Let’s Encrypt wildcard certificates generation, thanks to Nicolas Mengin (and thanks to xenolf to the initial ACMEv2 support in lego). This greatly simplifies certificate management as it avoids generating multiple sub-domains certificates. Now, it’s possible to generate root domain certificates, which will work for every sub-domain.
Note: ACME wildcard certificates can only be generated thanks to a DNS-01 challenge:
[acme]
# ...
[[acme.domains]]
main = "*.local1.com"
sans = ["local1.com"]
[[acme.domains]]
main = "*.local2.com"
# ...No more Let’s Encrypt rate limits :)
Open Tracing & Zipkin support

In microservice architectures, being able to reconstruct the elaborate journeys that transactions take as they propagate across a distributed system has become a minimum requirement for effective monitoring.
OpenTracing allows developers of application code, OSS packages, and OSS services to instrument their own code without binding to any particular tracing vendor.
We received a wonderful gift from Tristan Colgate-McFarlane (with the help of Michaël Matur) who implemented Open Tracing support, right into Traefik. Have a look at the documentation to get more details.
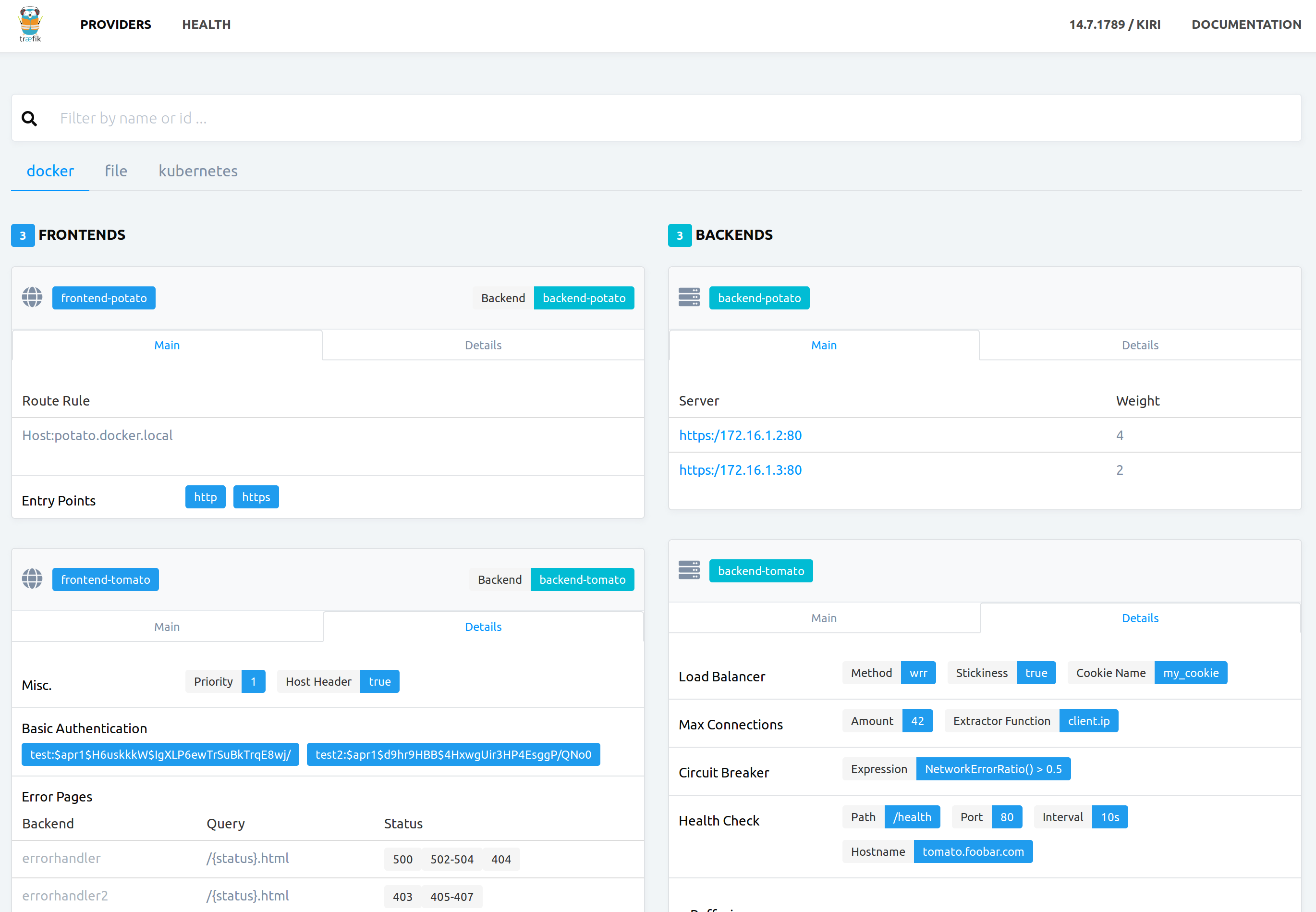
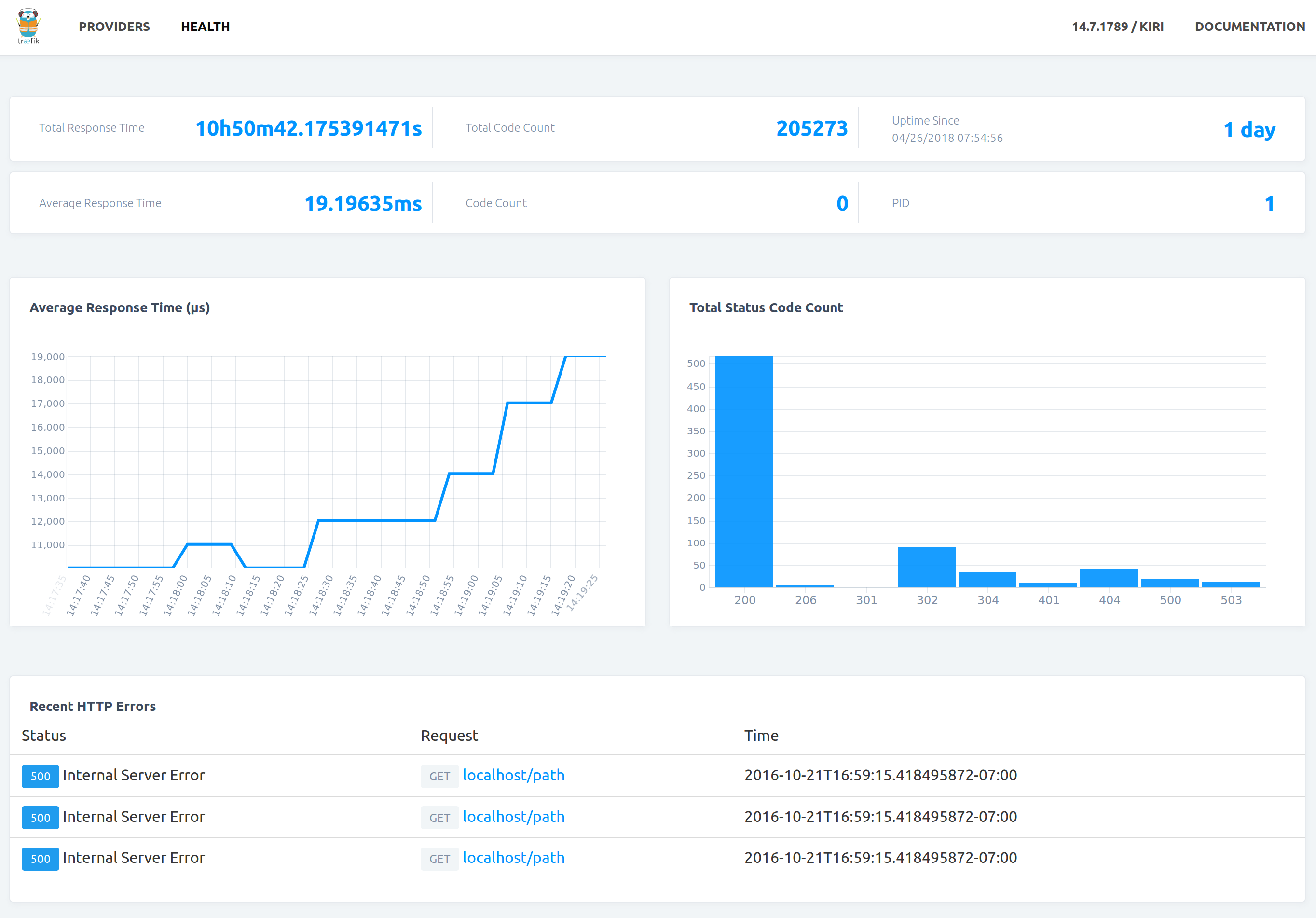
New Web UI
Jan Kuri & Ludovic Fernandez revamped our web UI, and we love how shiny it is. Amazing job!
TLS Certificates in Kubernetes Secrets
Another awaited feature, gopenguin added Kubernetes Secrets support for fetching TLS certificates. This enables Traefik to read the Kubernetes secret defined in an ingress resource via the tls property:
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: traefik-web-ui
namespace: kube-system
annotations:
kubernetes.io/ingress.class: traefik
spec:
rules:
- host: traefik-ui.minikube
http:
paths:
- backend:
serviceName: traefik-web-ui
servicePort: 80
tls:
- secretName: traefik-ui-tls-certAccess Logs Filtering

With the GDPR becoming real in EU, logging and storage of (potentially) personally identifiable information now need to be reduced in many organizations.
After a public proposal, Michaël Matur implemented a way to filter the content of access logs based on simple rules. Your can now keep, dropor redactfields and headers from your access logs. Take a look at our documentation to get a deeper insight.
Labels Homogenization
Probably one of the biggest refactoring of all time on Traefik, Ludovic Fernandez changed the way we manage labels internally, in order to homogenize labels on all providers. We now support all labels on all providers, no more specific code on this part 🎉
This will make it a lot easier to maintain, and we will be able to ship new features faster on all providers.
But that’s not all, check the whole changelog to get an idea of the awesome work that has been done on this release. Lots of bugs have been fixed and we also have been working on background refactoring tasks that will help us improving Traefik in future releases.
Grab the latest binary for Linux, Windows, Mac on Github or get the official Docker image!
docker pull traefik:v1.6.0 (or 1.6.0, v1.6, 1.6, tetedemoine)
docker pull traefik:v1.6.0-alpine (or 1.6.0-alpine, v1.6-alpine, 1.6-alpine, tetedemoine-alpine)The versioned documentation can be found on https://docs.traefik.io.
We are hiring developers and evangelists, try to solve our puzzle:containo.us/#jobs !
Traefik is still growing fast, we almost passed 15k stars on Github and 90M downloads!
We would love to hear your feedback on this new release. Join us on GitHub, Twitter or on the Community Forum!


