Manage your APIs at a Glance using the Traefik Enterprise API Portal
Every day, the number of APIs exposed by companies around the world is increasing.
APIs have become the standard method for companies to meet their B2B needs by providing customers with services in a seamless manner.
But the more APIs you need to expose, the more difficult it becomes to keep track of which APIs are exposed to which group, as well as maintain readability and testability standards across all your APIs.
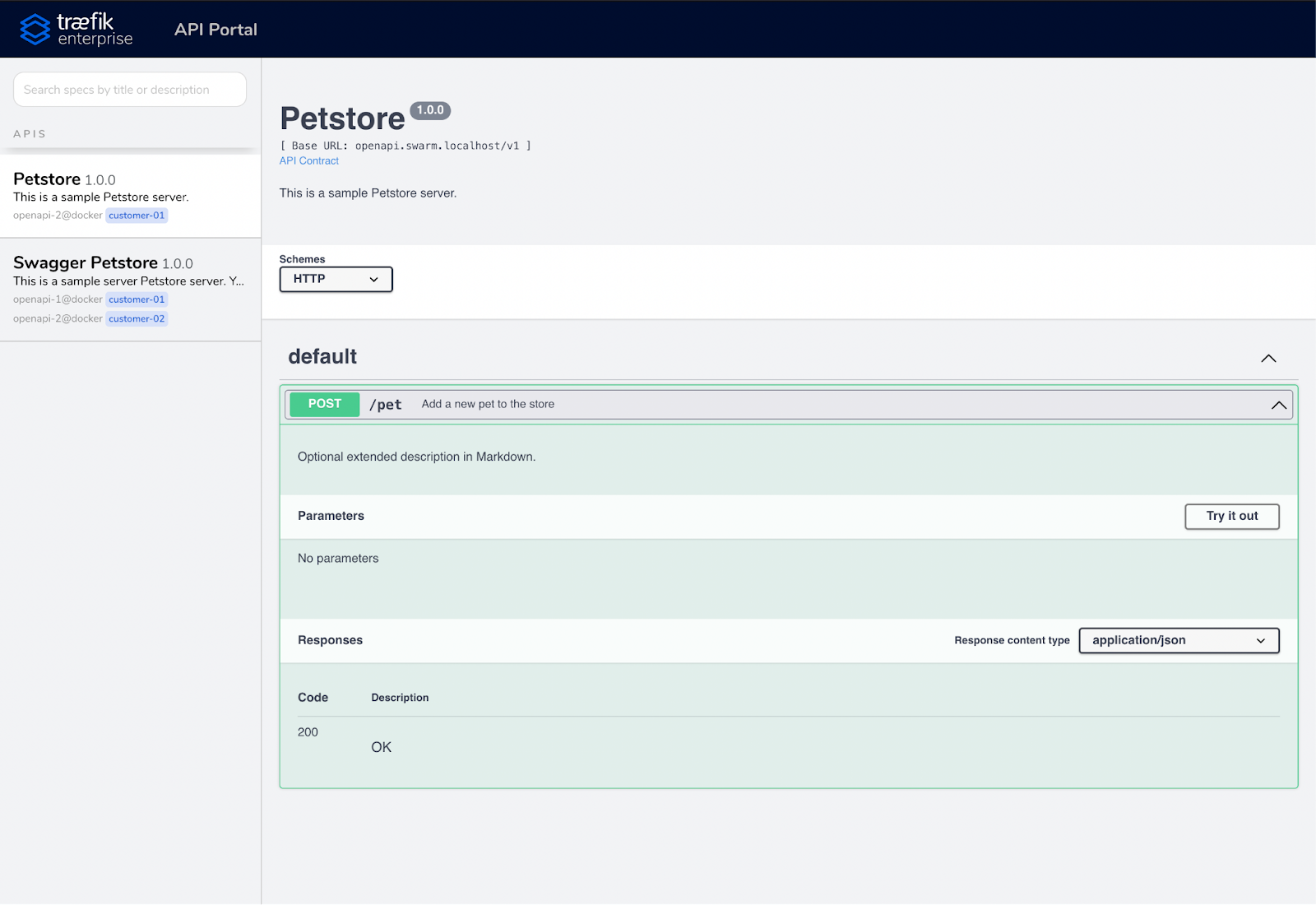
Thankfully, the OpenAPI Initiative allows you to standardize your APIs and make them readable and testable. The Traefik Enterprise API Portal uses the OpenAPI specifications to offer our customers a solution to expose their APIs in one place, creating a single source of truth for all their APIs in a fast and simple way.
In this article, I’ll explore the Traefik Enterprise API Portal and show you how to configure it for basic and more advanced needs.
Let’s get started!
A basic configuration for basic needs
Writing your API documentation and keeping it up-to-date is fine, but if you cannot share it in a straightforward way, it’s a loss of time.
With Traefik Enterprise, you can do so in the easiest way possible. Start with the initial configuration of the API Portal. After that, you can add and update all your APIs as needed and as often as necessary!
1. Enabling the API Portal
Once you have installed your Traefik Enterprise cluster into your infrastructure, you enable the API Portal using the standard Traefik Enterprise static configuration.
# static.yaml
providers:
kubernetesCRD: {}
entryPoints:
http:
address: ":80"
https:
address: ":443"
apiportal:
# Path to reach the OpenAPI specification file
path: /spec.json # YAML files are allowed too
Then, provide this new configuration to your Traefik Enterprise cluster using the CLI teectl.
teectl apply --file yourpath/static.yaml
Note: Kubernetes users that are installing Traefik Enterprise using the GitOps flow, can modify the ConfigMap which contains the static configuration.
2. Defining a router to reach your API Portal
The API Portal Access is managed in the same way as other Traefik services.
In order to allow your users to reach your API Portal, you just need to apply an IngressRoute on a Kubernetes cluster that targets the service internal@apiportal (which is the internal service that allows you to reach your API Portal):
echo '
# Traefik CRD to expose your API Portal on the domain apiportal.dev.localhost
apiVersion: traefik.containo.us/v1alpha1
kind: IngressRoute
metadata:
name: api
namespace: traefikee
spec:
routes:
- kind: Rule
match: Host(`apiportal.dev.localhost`)
services:
- kind: TraefikService
name: apiportal@internal
' | kubectl apply -f -
3. Reaching the API Portal
Once the API portal is configured, you can start exposing applications with an API contract using a JSON or YAML file that fits the Open API specifications.
There is only one requirement: store the file as defined in the configuration file (/spec.json in step 2).
Note: You can customize the path on each Service if necessary.
Going further
Now that you’ve seen the example of a basic configuration, let’s go one step further and take a look at how you can meet more advanced business needs.
Securing the API Portal
Exposing a portal that contains all your APIs only makes sense if you can maintain control over security best practices.
With Traefik Enterprise, you can secure access to your API Portal using an Authentication middleware — such as BASIC Authentication, LDAP, API Key, OIDC, or JWT — and limit its access with the rate-limit middleware.
echo '
# Traefik CRD to expose your API Portal on the domain apiportal.dev.localhost
# Secured using the Basic Authentication Method
apiVersion: traefik.containo.us/v1alpha1
kind: Middleware
metadata:
name: test-auth
spec:
basicAuth:
secret: authsecret
---
# Note: the password is not hashed, and is merely base64 encoded.
apiVersion: v1
kind: Secret
metadata:
name: authsecret
namespace: default
type: kubernetes.io/basic-auth
data:
username: dXNlcg== # username: user
password: cGFzc3dvcmQ= # password: password
–--
apiVersion: traefik.containo.us/v1alpha1
kind: IngressRoute
metadata:
name: api
namespace: traefikee
spec:
routes:
- kind: Rule
match: Host(`apiportal.dev.localhost`)
services:
- kind: TraefikService
name: apiportal@internal
middlewares:
- name: test-auth
' | kubectl apply -f -
Manage multiple API Portals
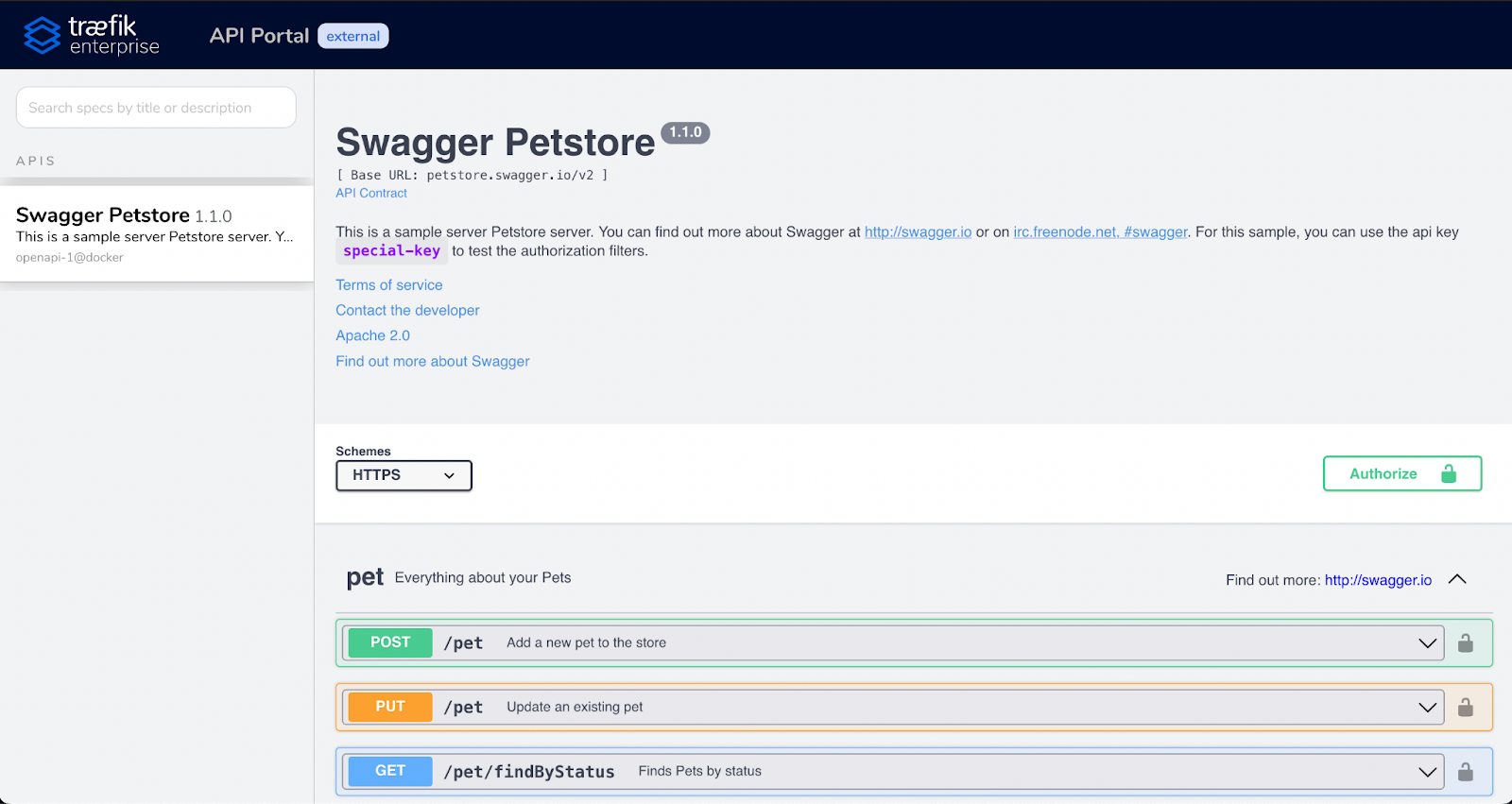
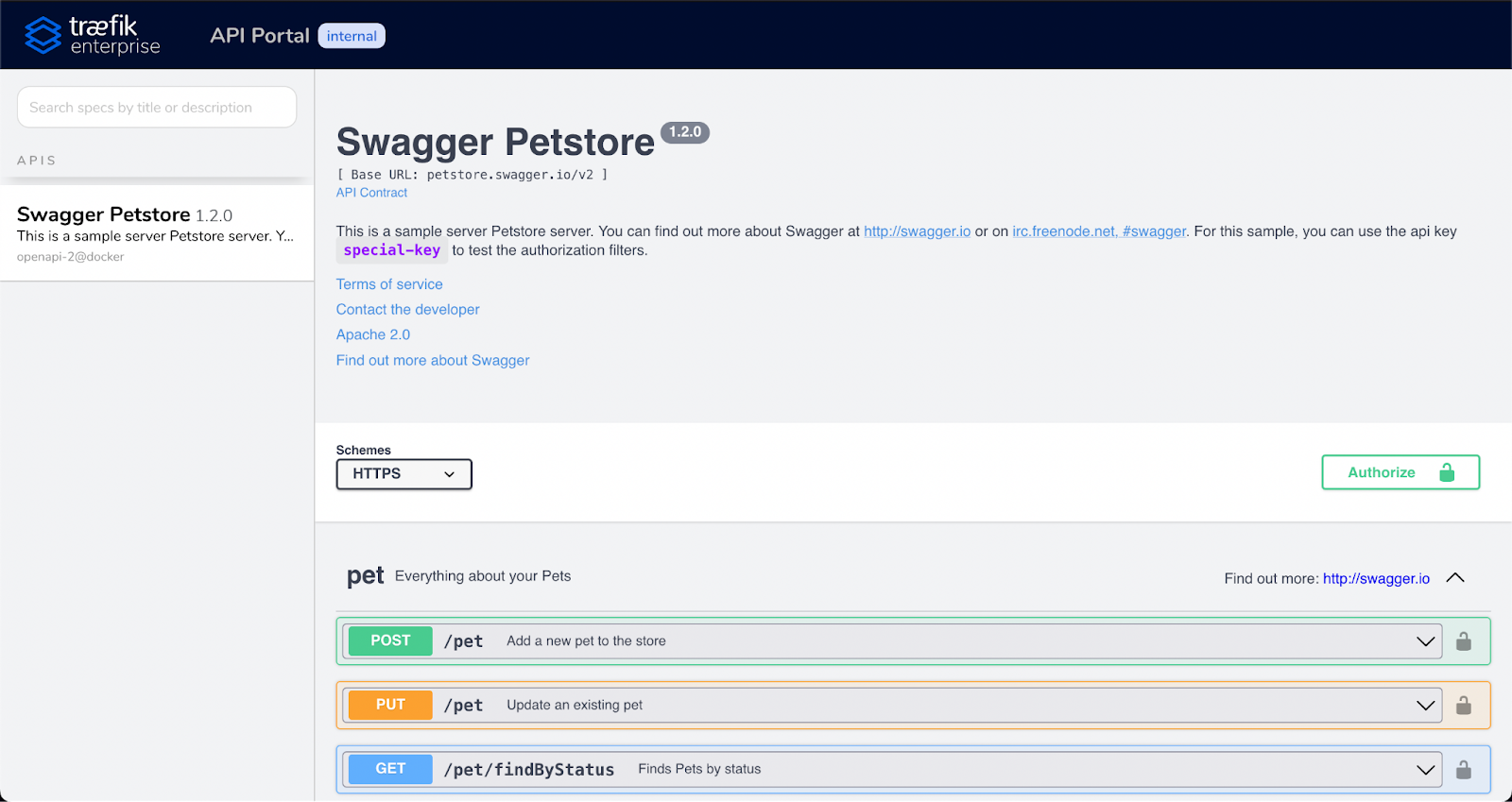
Part of the API lifecycle is the need to manage multiple versions of the same API simultaneously. On one hand, the current API version should be reachable by all your customers while, on the other hand, you need your development teams to have access to the next version for testing purposes.
The Traefik Enterprise API Portal accommodates this use case and more!
With the API Portal, you can manage multiple user groups and multiple instances at the same time.
Using the API Portal groups you can create multiple API Portals containing APIs that expose certain information to certain user groups, while you maintain a global overview of all APIs using the main API Portal UI. If you couple this feature with an authentication middleware you have the possibility to fine-grain your APIs management.
The example below describes the configuration of setting a Traefik Service to display its API only on the internal API Portal group.
apiVersion: v1
kind: Service
metadata:
name: api
annotations:
# Comment the external group to avoid displaying this API in your external API Portal
# traefik.ingress.kubernetes.io/service.apiportal.groups.external.path: "spec.json"
traefik.ingress.kubernetes.io/service.apiportal.groups.internal.path: "spec.json"
spec:
ports:
- name: api
port: 8080
selector:
app: traefiklabs
task: api
The following example exposes many versions of the same API on different API Portal groups (using multiple files on the same service).
apiVersion: v1
kind: Service
metadata:
name: api
annotations:
# Display the API version v1.1.0 on the external API Portal
traefik.ingress.kubernetes.io/service.apiportal.groups.external.path: "/v1.1/spec.json"
# Display the API version v1.2.0 on the internal API Portal
traefik.ingress.kubernetes.io/service.apiportal.groups.internal.path: "/v1.2/spec.json"
spec:
ports:
- name: api
port: 8080
selector:
app: traefiklabs
task: api
Wrapping up
With the Traefik Enterprise API Portal, you have a simple way to share your APIs with both your customers and your teams, or even provide dedicated portals for each of your customers. You can secure access at a glance and split the APIs between many portals.
The icing on the cake is that everything is done using configuration files, meaning all actions can be automated.
I’m also excited to say that we are continuously working on more enhancements for the API Portal that will satisfy even more business use cases in the future, so stay tuned!
In the meantime, if you are itching to try out the API Portal, I invite you to sign up for a free, 30-day trial of Traefik Enterprise.



